Market place: Production company
Industry: Pharmaceutics
Scale: 500+
Task: After the series of virus attacks and the actions of encoders that swept over Ukraine a customer asked us to analyze the network security vulnerability and to find a comprehensive solution to protect the enterprise networks in general. The audit has revealed some limitations: particularly, the productivity of the existing Firewall was low, the traffic inspection was not deep enough, it was impossible to integrate Active Directory and provide the retrospective analysis. Moreover, the company had constant difficulties with implementing security policies, and the network perimeter was broken.
We also conducted consultations with the Customer’s technical department, and have the common requirement for the new equipment, namely the acceptable speed of policies deployment on the device (the deployment time of policies on the old equipment took more than 15 minutes, which made the negative impact on the work productivity).
Technology: the solution to implement the reliable and fault tolerant customer network perimeter protection based on Cisco Firepower NGFW 21XX, 41XX was suggested.
Using FirePower provides the following features:
- Identification of the traffic from each client.
- Clear rules definition for any kind of traffic.
- Mandatory traffic inspection from the header down to the content.
- Incoming and outgoing traffic scanning to find malicious attachments.
- Strict control of Web-resources usage.
- Certain categories of web pages usage strict ban.
- Ability to create virtual private networks with remote offices.
- The ability of the retrospective analysis.
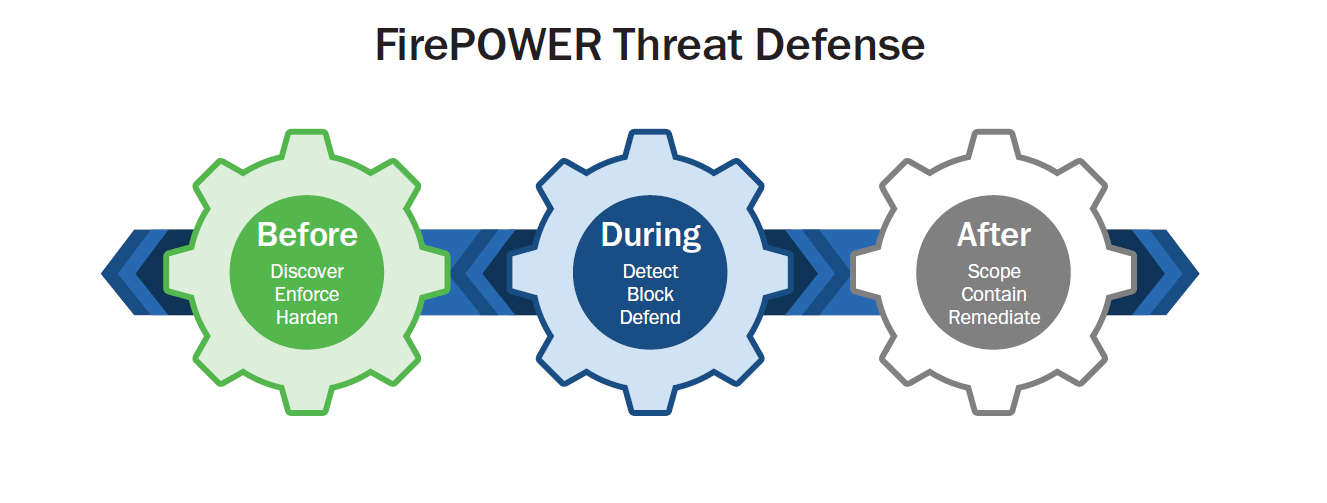
FirePower includes the functionality not only of the firewall but also of the IPS to be able to detect and repel attacks. In addition, it includes Advanced Malware Protection to protect against the malicious code, and URL filtering to control access to the Internet and VPN.
Result: The incorporation of a single FirePower NGFW device allowed us to eliminate all the defects of the customer’s perimeter protection, to track and block all unauthorized sessions and abnormal activity. The implemented security features have been integrated with the Active Directory and provide an opportunity for in-depth analysis of the network at the level of individual hosts and at the level of network devices. It has also become possible to simplify security policies management.